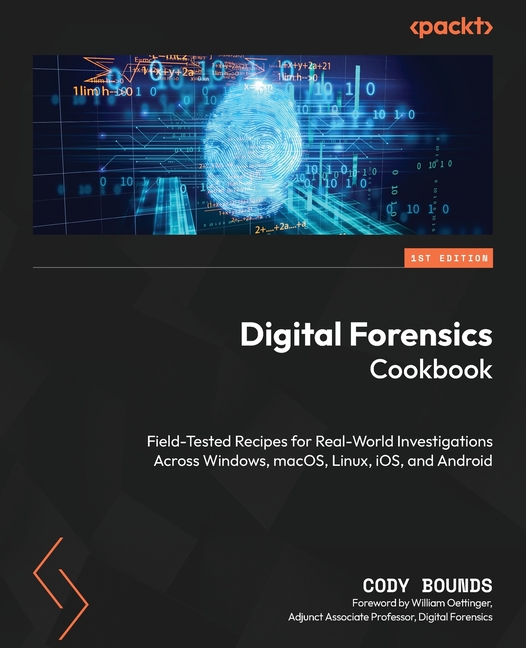
Digital Forensics Cookbook: Field-tested recipes for real-world investigations across Windows, macOS
$38.10
Payment received
We are registering your order now. Please stay on this page while we redirect you to the confirmation page.
- In Stock - Ship in 24 hours with Free Online tracking.
- FREE DELIVERY by Tuesday, April 28, 2026
- Secure checkout
- 15-day returns
- 24/24 Online
- Yes High Speed
- Yes Protection
Description
Learn the workflows professionals use to triage systems, uncover hidden activity, recover deleted evidence, crack encrypted containers, analyze Windows memory, and detect tampering using realistic hands-on forensic datasets.
Key Features:
- Master field-tested workflows for triage, acquisition, and cross-platform analysis
- Uncover hidden activity, recover evidence, defeat encryption, and detect tampering
- Build hands-on investigation skills using realistic datasets across major platforms
- Purchase of the print or Kindle book includes a free PDF ebook
Book Description:
Modern investigations and incident response efforts live and die by digital evidence. Digital Forensics Cookbook uses realistic datasets and practical workflows drawn from real investigations to uncover the truth hidden inside computers, mobile devices, and online accounts.
Rather than focusing on theory alone, this book moves you through the investigative process from triage and acquisition to artifact analysis, memory forensics, encryption challenges, malware triage, and detecting anti-forensic behavior. Along the way, you'll perform remote artifact collection, analyze evidence across Windows, macOS, Linux, iOS, and Android systems, investigate cloud-synced accounts, recover deleted data, manually carve evidence when tools fail, and identify attempts to hide or manipulate data.
As you progress through the book, you'll learn how to write and apply regular expressions and SQLite queries, build system timelines, baseline systems, automate analysis, verify findings across independent sources, generate custom password dictionaries to crack encrypted containers, detect metadata tampering designed to mislead investigators, and analyze Windows memory. By the end, you won't just know how to run forensic tools; you'll understand how investigators think, enabling you to turn scattered digital traces into clear, defensible conclusions.
What You Will Learn:
- Perform triage and acquire evidence during live investigations
- Collect artifacts remotely using incident response workflows
- Analyze evidence across Windows, macOS, Linux, iOS, and Android
- Recover deleted data and manually carve evidence when tools fail
- Crack encrypted containers using custom password dictionaries
- Use regex and SQLite queries to uncover hidden investigative clues
- Detect anti-forensic techniques and metadata tampering
- Analyze Windows memory using Volatility to uncover live artifacts
Who this book is for:
This book is for digital forensic investigators, incident responders, and security professionals who want to build practical investigation skills using real-world workflows and realistic datasets. It's also ideal for students and analysts entering the field who want hands-on experience recovering evidence, analyzing artifacts, and thinking like an investigator.
Table of Contents
- Targeted On-Scene Triage
- Network Intrusion Response and Remote Triage
- Physical and Cloud-Based Evidence Acquisition
- Microsoft Windows
- Apple macOS and Linux
- Apple iOS and Android
- Analysis Automation
- User Artifacts
- Manual Analysis and Techniques
- Overcoming Anti-Forensics
- Memory Forensics
Product Details
- Mar 31, 2026 Pub Date:
- 1805127551 ISBN-10:
- 9781805127550 ISBN-13:
- English Language
Fast moving this week
 Chainsaw Man Box Set
$93.87
Chainsaw Man Box Set
$93.87
 National Geographic Atlas of the World, 11th Edition
$183.40
National Geographic Atlas of the World, 11th Edition
$183.40
 Invincible Compendium Volume 2
$51.64
Invincible Compendium Volume 2
$51.64
 Naruto Box Set 2: Volumes 28-48 with Premium
$128.57
Naruto Box Set 2: Volumes 28-48 with Premium
$128.57
 Diary: Divine Mercy in My Soul (Revised)
$11.61
Diary: Divine Mercy in My Soul (Revised)
$11.61
 Netter's Anatomy Flash Cards
$41.84
Netter's Anatomy Flash Cards
$41.84
 It's Not You: Identifying and Healing from Narcissistic People
$18.57
It's Not You: Identifying and Healing from Narcissistic People
$18.57
 Amygdala
$49.86
Amygdala
$49.86
 Mom, I Want to Hear Your Story: A Mother's Guided Journal To Share Her Life & Her Love
$13.71
Mom, I Want to Hear Your Story: A Mother's Guided Journal To Share Her Life & Her Love
$13.71